Howto block mailservers using uncommon TLDs in hostname through Postfix
Reading time: 4 minutes
Blocking or blacklisting entire Top Level Domains (TLDs) used for hostname in email server setup can be a very effective solution to stop low reputation mail servers delivering mails to your email system(s).
As most email providers use common TLDs like .net, .com
or .de in their email setup, you can selectively block new or low reputation
TLDs and this way reducing a lot of unwanted emails.
If you are looking for a tutorial to blocking/blacklisting sender (users/clients) using specific TLD, this tutorial is the right one for you: Howto Block Entire TLDs in Postfix for Senders.
Setup
The setup on a single Postfix mail server is pretty straightforward and can be updated, extended, or removed at any time without big changes. As the hostname of a connecting email server is provided in the HELO/EHLO message, you have to target it on this step.
Create a File with Regexp Table Format
Regexp Tables are built-in Postfix and enabled by default. That’s why I prefer using Regexp instead of PCRE Table.
First of all, create a file called something like
/etc/postfix/helo_reject_domains and add the relevant Top Level Domain
(TLD) like .xyz, the word REJECT, and the message like We reject all email servers using .xyz domains.
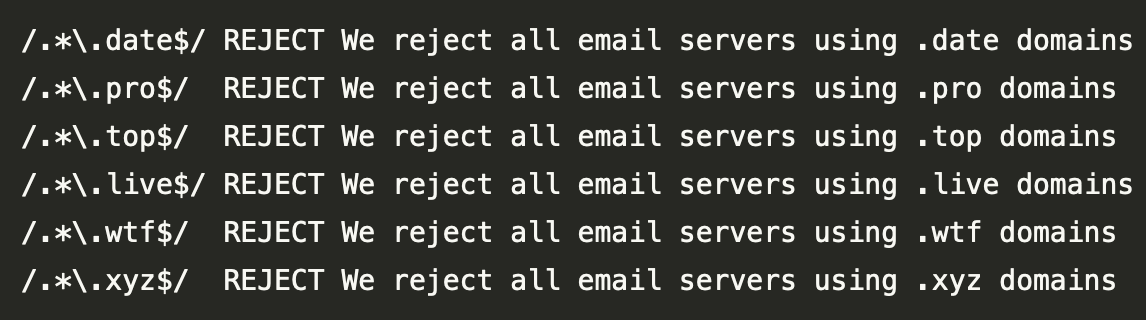
You define one regular expression for every TLD per line. Your
/etc/postfix/helo_reject_domains may look like this:
/.*\.date$/ REJECT We reject all email servers using .date domains
/.*\.pro$/ REJECT We reject all email servers using .pro domains
/.*\.top$/ REJECT We reject all email servers using .top domains
/.*\.live$/ REJECT We reject all email servers using .live domains
/.*\.wtf$/ REJECT We reject all email servers using .wtf domains
/.*\.xyz$/ REJECT We reject all email servers using .xyz domains
Now edit your Postfix main configuration /etc/postfix/main.cf and add a rule
to your smtpd_helo_restrictions at the relevant place:
smtpd_helo_restrictions = regexp:/etc/postfix/helo_reject_domains
WARNING: Some network providers use uncommon TLDs for the reverse DNS records
of client IPs. It is good practice to add this check after
permit_sasl_authenticated rule.
Your setup may look something like:
smtpd_helo_restrictions = permit_mynetworks, permit_sasl_authenticated,
regexp:/etc/postfix/helo_reject_domains, reject_invalid_helo_hostname,
reject_unknown_helo_hostname, permit
As the last step you have to reload/restart Postfix to enable this setup:
# using systemd
service postfix reload
# or just postfix
postfix reload
To block or not to block a whole TLD by mailserver hostname
Dependent on the use case of your server, it may be appropriate to block TLDs for a short or even longer period. Take a look at your logs, maybe a monitoring system, which can analyze and display such information.
By using MailMum and this way analyzing email traffic to the systems I’m responsible for, I could get the same insights as Brian Krebs. You can check Spamhaus World’s Most Abused TLDs to get a feeling, of what to look for.
Providing separated (virtual) servers for single customers which a specific user base, you can take advantage of this simple and pretty effective way to block senders using this technique.
Summary
Dependent on your mail systems setup, you can use TLD blocking by rejecting specific TLDs or even domains on HELO/EHLO to your servers using their hostname. It may be a valid solution for one use case and a wrong one for big providers hosting thousands of different customers with their different use cases on a system or even a cluster.
Using this technique, we could also identify a lot of invalid senders using different networks all over the world for the same purpose. The only drawback is, you have to monitor your systems for valid email providers and maybe remove the block listing on some time.
Based on our experience using our own MailMum Service, we could find a lot of abusive email servers using low reputation domain names as hostname from selected TLDs. For such domains you can see a lot of changes on reverse DNS records (rDNS) for the same IP.
Newsletter
See Also
- Howto Block Entire TLDs in Postfix
- Sending Test Emails from Shell
- Monitoring your Local Postfix Blacklist with Munin
- Blacklisting Single Hosts, IP Addresses, and even Networks in Postfix
- Whitelisting single Hosts, IP Addresses, and even Networks in Postfix